Which process represents the application-level allow list?
Refer to the exhibit.
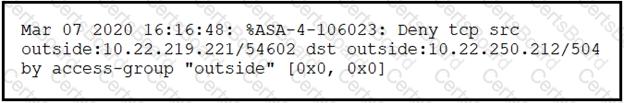
Which technology generates this log?
What is the difference between an attack vector and attack surface?
What is the difference between inline traffic interrogation and traffic mirroring?


