Switches maintain a CAM Table that maps individual MAC addresses on the network to physical ports on the switch.
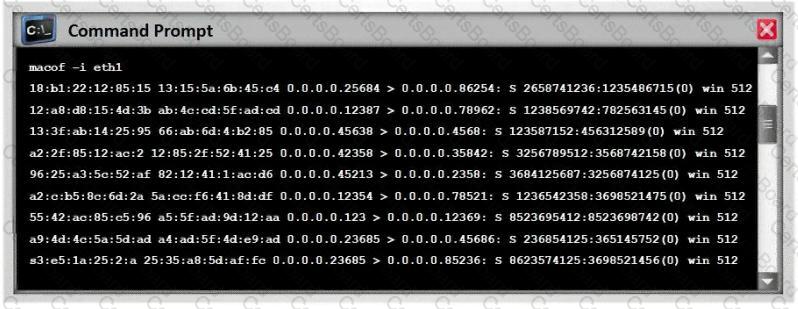
In MAC flooding attack, a switch is fed with many Ethernet frames, each containing different source MAC addresses, by the attacker. Switches have a limited memory for mapping various MAC addresses to physical ports. What happens when the CAM table becomes full?
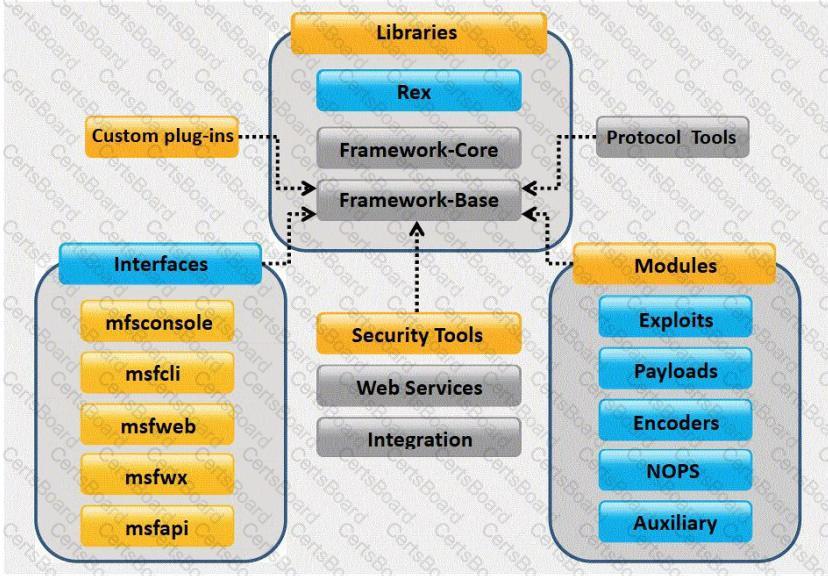
What framework architecture is shown in this exhibit?
You have chosen a 22 character word from the dictionary as your password. How long will it take to crack the password by an attacker?
In this attack, a victim receives an e-mail claiming from PayPal stating that their account has been disabled and confirmation is required before activation. The attackers then scam to collect not one but two credit card numbers, ATM PIN number and other personal details.
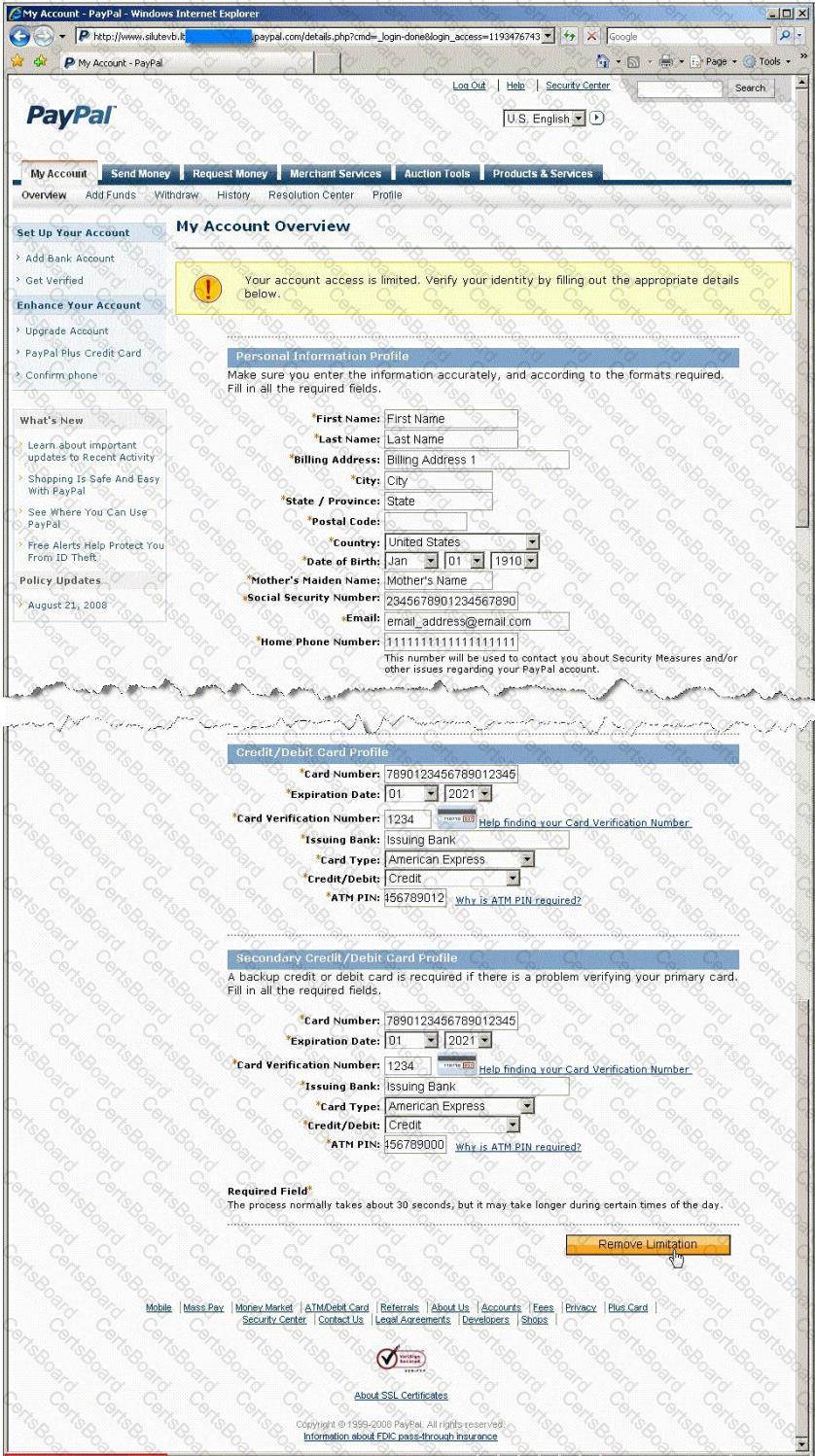
Ignorant users usually fall prey to this scam. Which of the following statement is incorrect related to this attack?


