A penetration tester wants to accomplish ARP poisoning as part of an attack. Which of the following tools will the tester most likely utilize?
A penetration tester is conducting an assessment on 192.168.1.112. Given the following output:
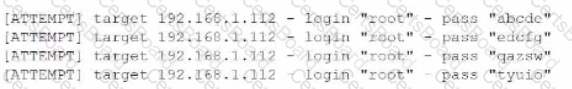
Which of the following is the penetration tester conducting?
Which of the following types of information would most likely be included in an application security assessment report addressed to developers? (Select two).
A security firm is discussing the results of a penetration test with a client. Based on the findings, the client wants to focus the remaining time on a critical network segment. Which of the following best describes the action taking place?


