Which of the following is a feature of virtualization that can potentially create a single point of failure?
During which of the following NIST risk management framework steps would an information system security engineer identify inherited security controls and tailor those controls to the system?
A security analyst is conducting traffic analysis and observes an HTTP POST to the company’s main web server. The POST header is approximately 1000 bytes in length. During transmission, one byte is delivered every ten seconds. Which of the following attacks is the traffic indicative of?
During a routine network scan, a security administrator discovered an unidentified service running on a new embedded and unmanaged HVAC controller, which is used to monitor the company’s datacenter:
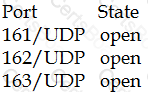
The enterprise monitoring service requires SNMP and SNMPTRAP connectivity to operate. Which of the following should the security administrator implement to harden the system?


