A company is implementing a new MFA initiative. The requirements for the second factor ate as folio.*.s
• It cannot be phished
• it must work as a second factor for laptop logins
• It must be something the user has
Which of the following solutions should the company choose?
A Chief Security Officer (CSO) is reviewing the organization’s incident response report from a recent incident. The details of the event indicate:
Which of the following would MOST likely have allowed the user to more quickly identify the unauthorized use of credentials by the attacker?
A company has deployed MFA Some employees, however, report they ate not gelling a notification on their mobile device Other employees report they downloaded a common authenticates application but when they tap the code in the application it just copies the code to memory instead of confirming the authentication attempt Which of the following are the MOST likely explanations for these scenarios? (Select TWO)
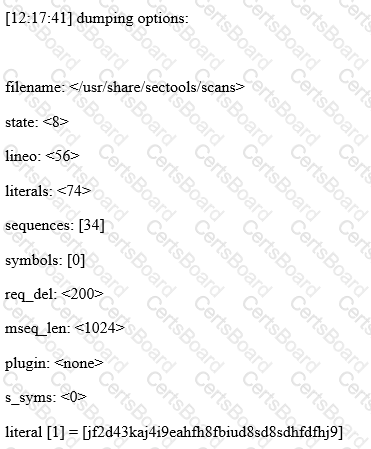
Given the following output from a security tool in Kali: