What is the communication channel established from a compromised machine back to the attacker?
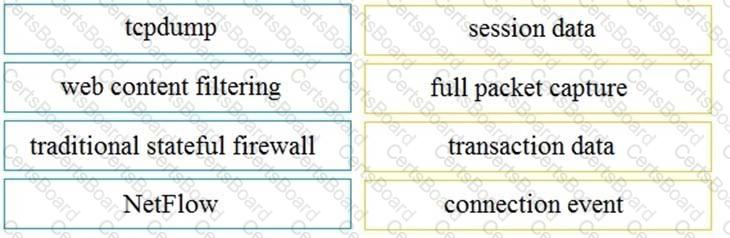
Drag and drop the technology on the left onto the data type the technology provides on the right.
Refer to the exhibit.
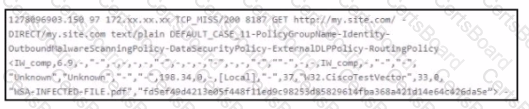
Which technology produced the log?
Refer to the exhibit.
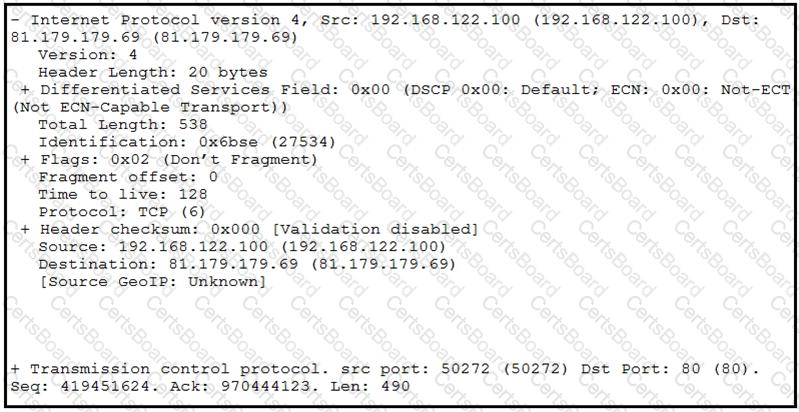
What should be interpreted from this packet capture?


