Which list identifies the information that the client sends to the server in the negotiation phase of the TLS handshake?
An engineer needs to configure network systems to detect command and control communications by decrypting ingress and egress perimeter traffic and allowing network security devices to detect malicious outbound communications. Which technology should be used to accomplish the task?
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
Refer to the exhibit.
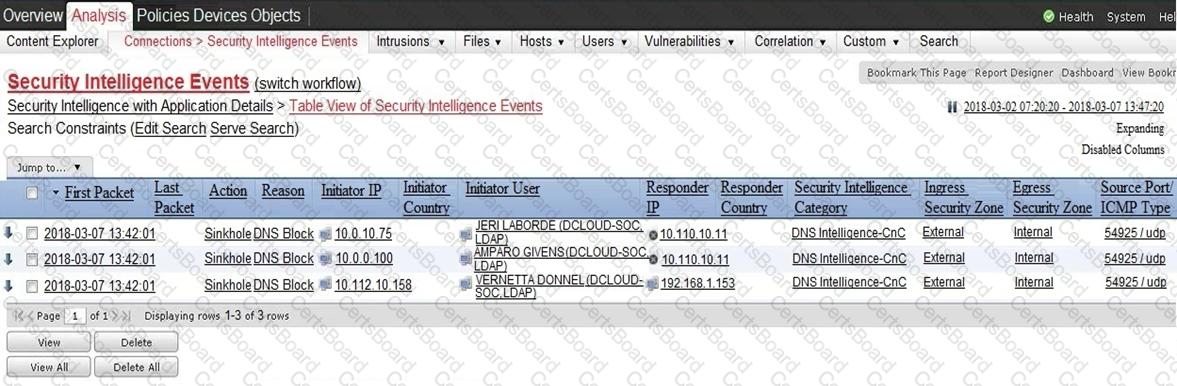
Which two elements in the table are parts of the 5-tuple? (Choose two.)


