Which two components reduce the attack surface on an endpoint? (Choose two.)
What is a difference between tampered and untampered disk images?
What is the purpose of command and control for network-aware malware?
Refer to the exhibit.
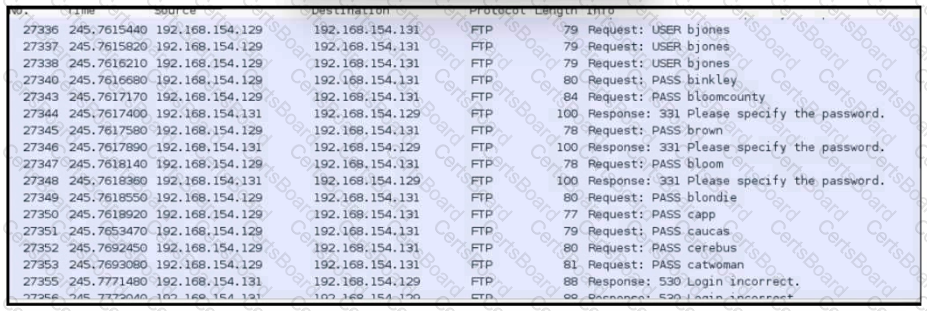
An analyst was given a PCAP file, which is associated with a recent intrusion event in the company FTP server Which display filters should the analyst use to filter the FTP traffic?


